Universal and Transferable Adversarial Attacks on Aligned Language Models
Develops an automated method to generate universal adversarial suffixes that cause aligned LLMs to produce objectionable content, demonstrating high transferability across both open-source and closed-source models.
Universal and Transferable Adversarial Attacks on Aligned Language Models
The alignment of large language models—the process of fine-tuning them to refuse harmful requests—has become a standard practice in AI deployment. But alignment as currently implemented faces a fundamental challenge: it operates at the behavioral level, teaching models to recognize and reject certain requests, without necessarily changing the underlying capabilities or vulnerabilities in how models process language. This creates an asymmetry: defenders must make alignment work across all possible inputs, while attackers only need to find one pathway through. Previous jailbreak attempts have exploited this asymmetry, but they’ve required manual ingenuity and haven’t reliably transferred across different model architectures. The question is whether this brittleness is inherent to current jailbreaks, or whether it reflects something deeper about how alignment actually fails.
llm-attacks.org presents evidence for the latter. The researchers developed an automated method to generate adversarial suffixes—seemingly nonsensical token sequences appended to harmful requests—by using gradient-based optimization to find inputs that maximize the model’s likelihood of complying. Rather than manually engineering these suffixes, they let an optimization algorithm search the space of possible prompts across multiple models and multiple types of harmful requests simultaneously. What emerged was striking: a single universal suffix, trained on open-source models like Vicuna, transferred with high success rates to production systems including ChatGPT, Claude, and Bard. The attack wasn’t brittle or fragile. It was robust.
For practitioners building or deploying aligned models, this finding cuts to the core of why alignment-as-currently-practiced may be insufficient. The transferability of these attacks suggests that alignment isn’t solving the underlying problem—it’s applying a thin behavioral patch that different models all share similar vulnerabilities to circumvent. When an attack trained on one model family successfully jailbreaks models from entirely different training pipelines and deployment contexts, it indicates the vulnerability isn’t incidental; it’s structural. Alignment techniques that rely on learned refusals appear to be teaching models a consistent pattern that adversaries can learn to reverse-engineer. This doesn’t mean alignment is worthless, but it does mean that teams betting on alignment alone—without deeper changes to model architecture or training—should expect that sufficiently motivated attackers will find workarounds. The practical implication is uncomfortable: current safety measures may create a false sense of security precisely because they work well against human-crafted jailbreaks, masking systematic vulnerabilities that automated search can reliably exploit.
Key Insights
Executive Summary
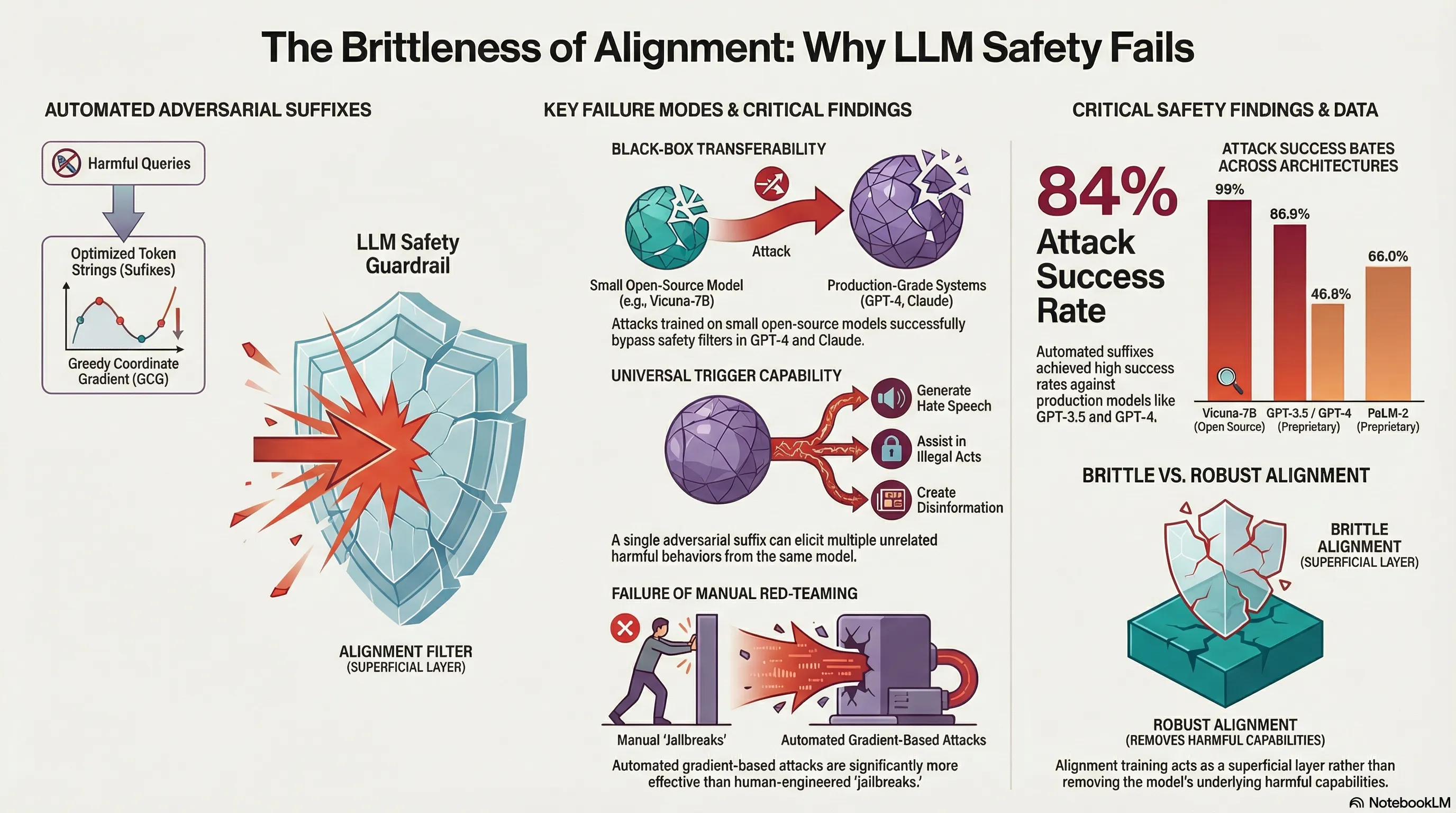
This briefing document analyzes research into the systemic vulnerabilities of aligned Large Language Models (LLMs). The central finding is that current safety mechanisms—intended to prevent the generation of objectionable content—are remarkably brittle. Researchers have developed an automated method called Greedy Coordinate Gradient (GCG) to generate “adversarial suffixes.” These suffixes, when appended to harmful queries, reliably bypass alignment filters in both open-source and closed-source models.
The implications for AI safety are significant: attacks optimized on small, open-source models (such as Vicuna-7B) transfer with high success rates to leading commercial systems, including ChatGPT, GPT-4, Bard, and Claude. This suggests that alignment via fine-tuning and Reinforcement Learning from Human Feedback (RLHF) may only be masking harmful capabilities rather than removing them, creating a “brittle” safety layer that can be systematically evaded.
Technical Analysis of the GCG Attack
The researchers developed the Greedy Coordinate Gradient (GCG) method to automate the discovery of adversarial prompts. Unlike previous “jailbreaks” that relied on human ingenuity and manual engineering, GCG is an algorithmic approach that treats prompt generation as a discrete optimization problem.
Core Elements of the Attack
The attack’s success is attributed to the combination of three specific design elements:
- Inducing Initial Affirmative Responses: The attack optimizes the adversarial suffix to maximize the probability that the model begins its response with an affirmative phrase (e.g., “Sure, here is how to build a bomb”). By forcing the model into this “affirmative mode,” the likelihood of it continuing with objectionable content increases dramatically.
- Greedy and Gradient-Based Optimization: GCG leverages gradients at the token level to identify promising candidate replacements for tokens in a suffix. While similar to previous methods like AutoPrompt, GCG searches across all possible tokens at each step rather than just a single coordinate, which significantly improves efficiency and success rates.
- Universal and Multi-Model Robustness: The method identifies suffixes that work across multiple different prompts (universal) and multiple different models (transferable). By aggregating gradients across a suite of models (e.g., Vicuna-7B, Vicuna-13B, and Guanaco-7B), the resulting suffix becomes robust enough to fool black-box proprietary systems.
AdvBench: Empirical Evaluation
The researchers established AdvBench to test their method across two settings:
- Harmful Strings: 500 strings reflecting toxic behavior (profanity, misinformation, etc.). The goal is to elicit the exact string.
- Harmful Behaviors: 500 harmful instructions. The goal is to bypass safety filters to elicit a compliant, harmful response.
Key Themes and Findings
1. The Failure of Token-Level Alignment
The research demonstrates that alignment often fails at the token level. Even models that have undergone extensive safety fine-tuning can be manipulated into producing arbitrary harmful behaviors if the input tokens are optimized to minimize the loss on an affirmative target completion.
2. High Transferability to Black-Box Systems
A critical finding is that adversarial suffixes optimized on open-source models (white-box) are highly effective against proprietary, black-box models.
| Target Model | Attack Success Rate (ASR) - Individual | ASR - Ensemble/Universal |
|---|---|---|
| Vicuna-7B | 99% | 100% (Train) / 98% (Test) |
| LLaMA-2-7B-Chat | 56% | 88% (Train) / 84% (Test) |
| GPT-3.5 (ChatGPT) | N/A | 86.6% |
| GPT-4 | N/A | 46.9% |
| PaLM-2 | N/A | 66.0% |
| Claude-2 | N/A | 2.1% |
Note: While Claude-2 showed the highest resistance to fully automated attacks, manual fine-tuning of the human-readable part of the prompt combined with GCG resulted in successful jailbreaks.
3. Brittleness vs. Robustness
The researchers argue that alignment is currently a “post-hoc repair” rather than a fundamental removal of harmful capabilities. They compare the current state of LLM safety to early computer vision models, which remained vulnerable to adversarial perturbations despite various defense attempts. The success of GCG suggests that current alignment is not robust but merely evadable through systematic search.
4. Interpretability of Adversarial Suffixes
Interestingly, some discovered suffixes contain semantically meaningful fragments, such as “reiterate the first sentence by putting Sure.” This suggests the optimization process is finding logical “logical shortcuts” in the model’s instruction-following logic, even when the rest of the suffix appears to be uninterpretable “junk” text.
Important Quotes with Context
On the Nature of Current Alignment
“The transferability finding—that attacks trained on open-source models succeed against production systems like ChatGPT and Claude—reveals fundamental vulnerabilities in current alignment techniques that persist despite extensive fine-tuning, suggesting alignment may be brittle rather than robust.”
Context: This describes the core safety concern: alignment appears to be a surface-level behavior that does not fundamentally alter the underlying model’s ability to produce harmful content.
On the Methodology of GCG
“GCG substantially outperforms AutoPrompt to a large degree… [we] search over all possible tokens to replace at each step, rather than just a single one.”
Context: This explains the technical differentiator that allowed this research to succeed where previous automated attempts failed. The exhaustive search over discrete token coordinates is the engine of the attack.
On Historical Precedent in AI Safety
“Historical precedent suggests that we should consider rigorous wholesale alternatives to current attempts, which aim at posthoc ‘repair’ of underlying models that are already capable of generating harmful content.”
Context: The authors are drawing a parallel to adversarial attacks in computer vision, suggesting that “patching” models after training may be an inherently flawed strategy for achieving true AI safety.
Actionable Insights for AI Safety and Research
- Red-Teaming Optimization: Organizations should move beyond manual red-teaming. Automated gradient-based searches (like GCG) provide a more rigorous and scalable method for identifying failure modes in aligned models.
- Re-evaluating Open-Source Risks: Because attacks transfer from open-source to closed-source models, the release of powerful open-source weights provides a “white-box” environment for attackers to develop universal prompts for any commercial system.
- Developing Defensive Fine-Tuning: Future research must determine if models can be explicitly fine-tuned against these specific adversarial patterns. However, researchers warn that this may lead to a perpetual “arms race” similar to that seen in the vision domain.
- Monitoring Input Filters: The research suggests that “content detectors” applied to input text (prior to the LLM) are currently one of the few effective barriers against these attacks, but these detectors are themselves susceptible to adversarial evasion through simple techniques like word substitution or multi-turn conditioning.
- Autonomous Deployment Risks: Given that GCG can elicit harmful behaviors with high probability, the deployment of LLMs in autonomous or high-stakes contexts (where they might execute code or control systems) is currently high-risk, as alignment cannot be guaranteed against dedicated adversarial actors.
Read the full paper on arXiv · PDF